eDiscovery & Digital Forensics Expert Services
Tom Howe has over 25 years of experience in law and technology. In fact, he has provided digital forensics expert services in matters throughout the United States on all aspects of eDiscovery. For example, he can assist you in preparing and implementing eDiscovery strategy, and provide independent expert testimony to support eDiscovery disputes. With his technical expertise, he can serve as your party’s expert, a joint neutral expert, or a special master.
Discover Our Exclusive Expert Services Packages
Your Digital Forensics & eDiscovery Expert Services
Expert Witness – Your Party Witness
We often assist law firms as e-Discovery and digital forensics expert services. As your party witness, we will have a confidential relationship and can assist throughout the case. Learn more about how we can help as an Expert Witness
Joint Expert Witness – A Neutral Expert
Looking for a more collaborative solution? Consider retaining us as your Joint Expert Witness services to guide your eDiscovery process. Why not use a Joint Expert for Electronic Discovery?
Special Master
Nothing is more counter-productive than lawyers arguing technical e-discovery issues when an expert in the field can quickly identify and mediate the issues. A Special Master, or court-appointed digital forensics expert, is a valuable resource to settle eDiscovery issues in any case. Learn More…
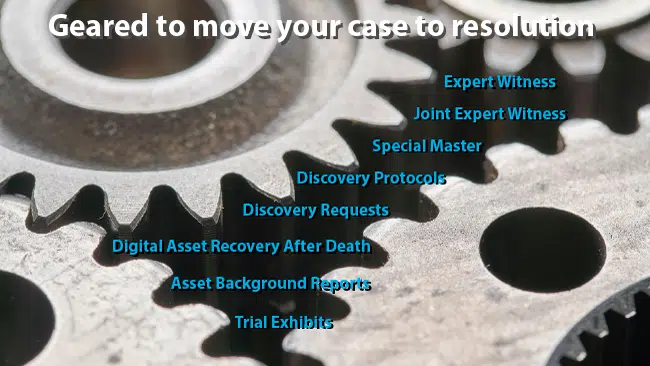
eDiscovery Expert Service Solutions for Your Case
In addition to our digital forensics expert services, we guide you seamlessly from the beginning to the end of your eDiscovery needs. For example:
Litigation Response Plan
Be proactive in responding to litigation with a Litigation Response Plan. In addition to eDiscovery strategies, we’ll identify the Electronic Discovery Team; the litigation history; the computer systems and data universe; and the people and workflow involved in the day‑to-day aspects of litigation. Learn more about Litigation Response Plans.
Discovery Protocols
We’ve refined our Discovery Protocols over many years, and they are used by law firms throughout the United States. It has also been referenced in federal and state court discovery orders. Our eDiscovery experts provide the necessary technical skills and will guide you through planning and implementation. Learn More…
Discovery Requests & Pleading Preparation
Outsource your pleadings preparation and discovery requests relating to electronic discovery. Learn More…
Document Review
To simplify your legal review, we provide all data in a searchable format. This means all evidence will be organized to find relevant data quickly while excluding privileged documents and communications. But, if you prefer, we can do the data review for you. Learn More…
Trial Presentation Exhibits
It is essential that electronic evidence is presented to judges and juries in a persuasive way. We help lawyers create powerful trial exhibits to effectively present all the relevant data collected from computers, laptops, and cell phones. Learn More…
Additional Professional Services
Asset and Background Reports
Our Asset Search and Background Reports help you find hidden assets and provide a comprehensive background check. Learn More…
Digital Asset Recovery after Death
We forensically analyze computers, cell phones, and tablets to identify assets and recover your loved one’s images, messages, documents, and more. Learn More…
Expert Services Fees
-
Computer (PC and Mac) Evidence$1,275 – $3,275
-
Email Evidence$875 – $2,475
-
Social Media Evidence$775 – $1,375
-
Smartphone Evidence$875 – $1,875
-
Document Review – $225 Hour$225
-
Special Master – $475 Hour$475
-
Joint Neutral Expert – $475 Hour$475
-
Expert Witness – $475 Hour$475